Quantum computing is a fascinating and rapidly evolving field. Here are three interesting facts about it.
Is Bitcoin a Ponzi Scheme?
In this post we take a look at the nature of Bitcoin, compare it with the characteristics of a Ponzi scheme, and try to give an answer to the question.
3 Must-Reads on the CO2 Emission Surge in 2023
As 2023 wraps up, it’s clear that we’ve hit a new milestone in CO2 emissions — and not the kind we can be proud of.
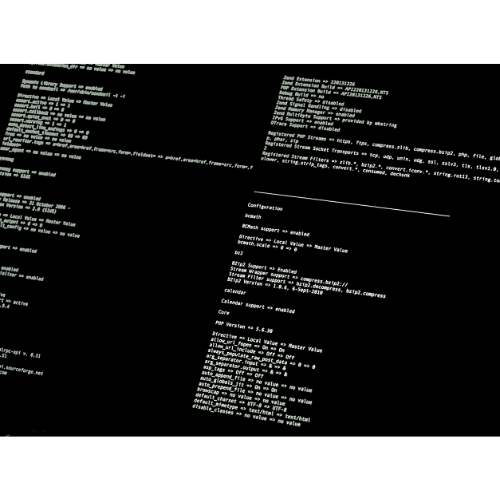
Guide to Windows CMD commands
In this guide, we will explore the most useful and important CMD commands that every Windows user should know. It doesn’t matter if you are a computer expert or a beginner venturing into the world of the command line for the first time.
November 28, 2012: Bitcoin’s First Halving Event
On November 28, 2012, an event of unprecedented significance occurred in the world of cryptocurrency: the first Bitcoin halving. It was on this day that the reward per block for mining Bitcoin was reduced from 50 to 25 Bitcoins.
Understanding the Total Cost of Ownership for an IIoT Solution
Deploying an Industrial IoT solution isn’t just about technology, it’s also about understanding the full financial costs of deploying such a solution. Let’s break down the Total Cost of Ownership (TCO) for an IIoT solution.
Cryptocurrency Mines
Cryptocurrency mining is the process of validating cryptocurrency transactions and adding these transactions to the public ledger called the blockchain. In return for this work, miners receive a reward in the form of new cryptocurrencies.
Edge Computing in 2023
Edge Computing is set to revolutionize various sectors with its capability to process data closer to where it’s generated, reducing latency and bandwidth use. Here are several key trends and insights on Edge Computing gathered from multiple sources.
Double Spend Attack: Spending the Same Crypto Twice
A Double Spend Attack is a critical potential flaw in a digital cash scheme where a user attempts to spend a single unit of a digital currency more than once. This can cause serious complications, leading to fraudulent transactions and loss of trust in the system.